Executive Summary
DrugHub Market functions as a decentralized hidden service ecosystem operating exclusively within the Tor network architecture. Observers note that the platform focuses heavily on digital commodities, privacy-centric commerce, and strict communication protocols.
Unlike traditional e-commerce frameworks, this system completely removes conventional credential mechanics in favor of cryptographic identity verification. The platform aims to provide a resilient, untraceable environment resilient to network interruptions and operational downtime.
Historical Timeline
Network Genesis
Initial deployment of the core onion routing logic and base database schemas. The platform established its first connections via primary seed nodes.
Cryptographic Enforcement
Implementation of strict PGP-only authentication. Conventional password databases were purged to minimize data retention liabilities.
DDoS Resiliency
Major architectural overhaul integrating proof-of-work captchas and mirrored load-balancing to combat aggressive network saturation attacks.
Architecture
- Ledger Integration Exclusive Monero (XMR) support utilizing subaddress generation per transaction to inhibit blockchain heuristic analysis.
- Transaction Logic Multisignature 2-of-3 escrow protocols are standard, ensuring funds require consensus before final release to distributing nodes.
- Wallet Configuration Walletless design implementation. The system does not hold central balances, reducing the threat profile of database compromises.
Community Stats
Commercial entities distributing on the network are subject to rigorous verification procedures, including the mandatory posting of cryptographic bonds. Observers note a high reputation for community dispute resolution and node stability.
Platform Interface Preview
The following exhibits document the structural layout and interactive flow of the system. These records are maintained for analytical indexing of hidden service topologies.
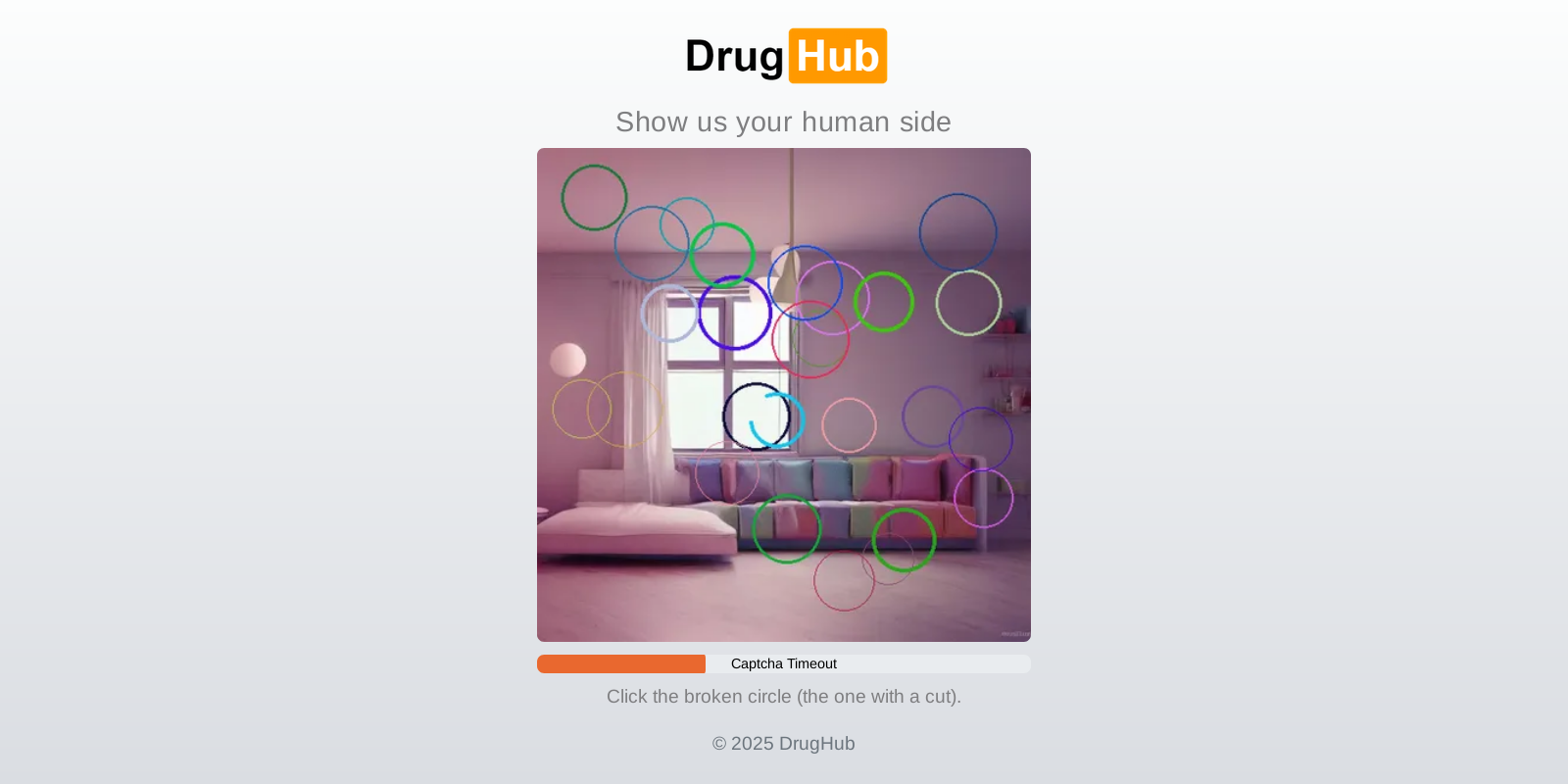
Fig 1. DDoS Protection Screen
Clock verification and request validation sequence initiated prior to routing assignment.
Fig 2. User Login Interface
Implementation of cryptographic authentication demanding PGP decryption challenges.
Fig 3. Account Registration Page
Identity generation requiring strict key formatting and public key broadcast.
Fig 4. Main Market Dashboard
Structural layout of categories, communication relays, and node system metrics.